Raspberry Pi backup veloce sd card
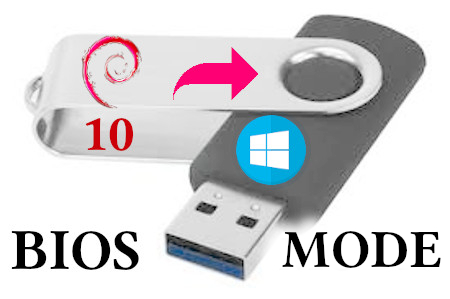
Guida su come ottenere un backup veloce e funzionante del proprio sistema. Per chi utilizza un Raspberry Pi, con tutto il sistema installato su sd card, è buona regola avere un backup completo, per poter ovviare velocemente ad una ipotetica perdita/rottura dei dati sulla sd card. A difesa delle sd card, io posso tetimoniare, essendo possessore di tanti Raspberry Pi, fin da maggio 2012, che se si acquistano le migliori, difficilmente si rompono. Io per i vari utilizzi, ho speso di più per la sd card che per il Raspberry Pi. I metodi di backup a cui io mi riferisco utilizzano i comandi dd e rsync. Il classico metodo più utilizzato e sicuro è il seguente:
Metodo 1)
Estrarre dal Raspberry Pi la sd card di origine e creare un file img
sudo dd bs=4M if=/dev/sdx of=PiOS.img
Ripristinare su sd card di backup:
sudo dd bs=4M if=PiOS.img of=/dev/sdx
Con il metodo sopra i tempi sono più lunghi, poichè dd, clona tutto. Esistono altri metodi simili, aggiungendo la compressione, ma a me non soddisfano.
Metodo 2)
Questo metodo è quello che utilizzo io, e può essere eseguito sia a caldo, sia estraendo la sd card clonandola. Per questo metodo si utilizza dd, solo per quanto riguarda le tabelle delle partizioni, e la partizione di boot, tutto il resto lo farà rsync copiando velocemente il contenuto della rootfs.
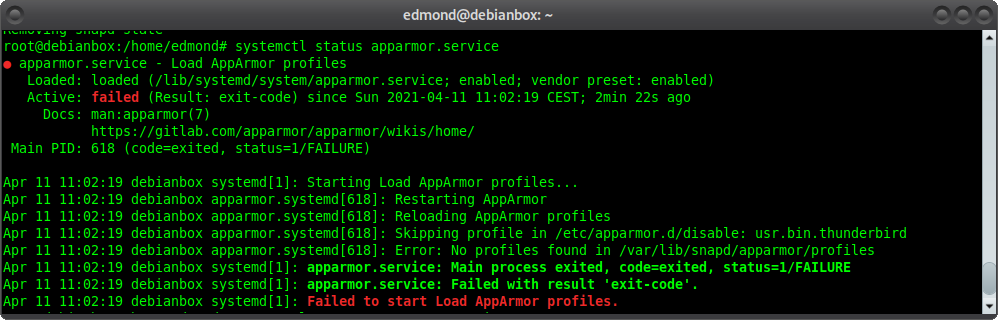
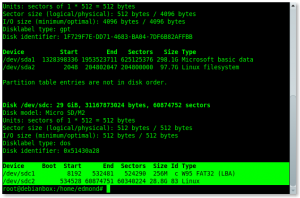
Inserire su pc la sd card da cui effettuare il backup e raccogliere informazioni:
sudo fdisk -l
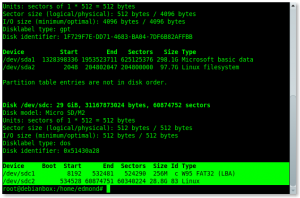
esistono 2 partizioni, nel mio caso, /dev/sdc1 di boot ed /dev/sdc2 rootfs. Bisogna prendere nota delle 2 voci start, 8192 e 534528, cosicchè da creare una identica tabella delle partizioni, contenendo tutti i files di boot:
sudo dd bs=4k count=$((8192/8)) if=/dev/sdc | gzip >boot-img.gz
sudo dd bs=4k count=$((534528/8)) if=/dev/sdc | gzip >rootfs-img.gz
Adesso dobbiamo copiare in una cartella il contenuto di /dev/sdc2 utilizzando rsync:
sudo apt install rsync
sudo mkdir /mnt/{dati,rootfs}
sudo mount /dev/sdc2 /mnt/dati/
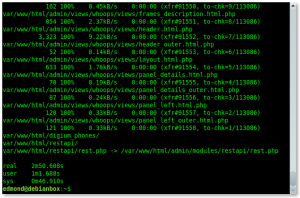
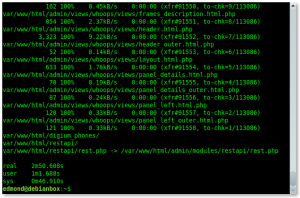
sudo rsync -aHAXSP /mnt/dati/ /mnt/rootfs/
sudo umount /dev/sdc2
Basta. Finito. Tempo totale meno di 3 minuti:
Inserire la sd card di backup:
Azzerare tabella partizioni:
sudo dd count=1 bs=512 if=/dev/zero of=/dev/sdc
creazione della tabella delle partizione come da sd card origine:
sudo zcat boot-img.gz | sudo dd bs=4k iflag=fullblock of=/dev/sdc
sudo partprobe /dev/sdc
sudo zcat rootfs-img.gz | sudo dd bs=4k iflag=fullblock of=/dev/sdc
sudo partprobe /dev/sdc
formattare la seconda partizione in ext4:
sudo mkfs.ext4 -L rootfs /dev/sdc2
mount e copia :
sudo mount /dev/sdc2 /mnt/dati/
sudo rsync -aHAXSP /mnt/rootfs/ /mnt/dati/
umount ed attendere, può volerci qualche minuto:
sudo umount /dev/sdc2
Tempo totale 15 minuti circa. A questo punto se tutto è andato bene, abbiamo una copia perfetta della sd card di origine. Questo metodo funziona anche in presenza di database.
Raspberry Pi backup veloce sd card
enjoy 😉
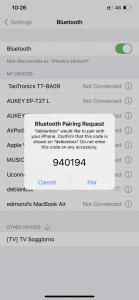 Come ascoltare la musica nel telefono tramite le casse del pc Debian Gnu Linux
Come ascoltare la musica nel telefono tramite le casse del pc Debian Gnu Linux